See Footage From Sea Otter Pup Un'a's Admit Exam
Jul. 16th, 2025 12:27 pmVia Alaska SeaLife Center, which writes:
It’s hard to believe how far little Un’a, the orphaned sea otter pup admitted in May 2025, has come.
When she was first rescued, she was fragile and underweight. Every feeding and time resting was critical in those early days, as you’ll see in this video. We’ve been busy responding to a wave of harbor seal patients, but Un’a has been quietly making big strides behind the scenes.
Now, just over a month into care, she’s thriving: healthy, eating solids, and showing off her playful personality. She’s definitely earned her moment in the spotlight!
Secret police slush fund is gonna be SO corrupt
Jul. 15th, 2025 08:52 pmJust a Sleepy Sea Otter Pup
Jul. 15th, 2025 11:04 amVia Alaska SeaLife Center, which writes:
Our “Homer boy” otter patient is resting, recovering, and reminding us to slow down…
Do you see the breeze on the pup's fur? That is from a fan, which we use to help ensure that his coat gets thoroughly dry and captures extra air to help keep him warm—something that Mom would achieve by blowing into his coat.
‘Perversion of Justice’ revisited
Jul. 15th, 2025 03:12 amHappy First Rescueversary, Luna!
Jul. 14th, 2025 12:04 pm
Via Vancouver Aquarium, which writes:
Happy first rescueversary to sea otter Luna! Found separated from her mother on Vargas Island near Tofino, BC on this day in 2024, she was deemed non-releasable and transferred to the Vancouver Aquarium alongside pup Tofino later that year.
Demonic Ox spoiler discussion space
Jul. 13th, 2025 01:55 pmClick back to the immediately prior post for all the publication details.
As of today Amazon, B&N, and Apple Books US are known to have the book up. Kobo and Google Play Books seem to be lagging, and there's something odd going on with Apple worldwide versus our Spectrum editions that we haven't sussed out yet. I will update when there's something new to say.

Have fun!
Ta, L.
(As always, word of mouth is the lifeblood of my career, so mentions of the story out and about elsewhere are very much appreciated.)
posted by Lois McMaster Bujold on July, 13
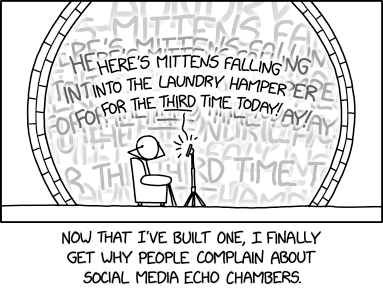
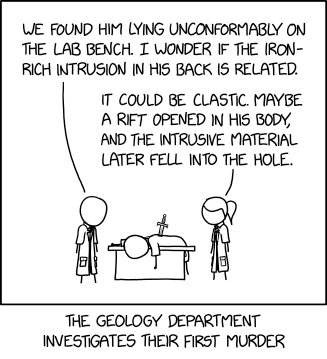
A terrible comic about baseball
Jul. 12th, 2025 05:54 pmOn social media recently, it was “Make a Terrible Comic Day.” Since making terrible things comes naturally to me, I decided to participate! Here is my contribution.

It was fun to draw this by hand, which I am quite out of practice at.
You can see more “terrible comics” using the #makeaterriblecomicday2025 hashtag on Bluesky and Instagram!
LBCF: Fizzbinsationalism
Jul. 11th, 2025 09:12 pmDemonic Ox arrives today!
Jul. 11th, 2025 11:29 amAmazon Kindle is first out the gate:
https://www.amazon.com/dp/B0FHBMR3DN
Not yet up, but pending:
Kobo, Google Play Books, and Apple Books are interesting if you search by my name, because they each carry so many foreign language titles, if you scroll down. (Amazon ditto, I suppose.) These pages should populate in due course, though it may take a while for a new entry to sift to the top:
https://www.kobo.com/us/en/search?que...
https://play.google.com/store/info/na...
https://books.apple.com/us/author/loi...
Direct Apple US link: https://books.apple.com/us/book/the-a...
(Some readers are reporting problems finding my Spectrum titles on Apple outside the US, as per Bo, below. If you are one, chime in in the comments with details. Though I suppose we should give it a bit more time to propagate...)
B&N Nook, same deal:
https://www.barnesandnoble.com/s/lois...
Direct link is up! : https://www.barnesandnoble.com/w/the-...
To recap:

The Adventure of the Demonic Ox
When sorcerer Learned Penric hears of the suspected demonic possession of an ox at his brother-in-law’s bridgebuilding worksite, he thinks it an excellent opportunity to tutor his adopted daughter and student sorceress Otta in one of their Temple duties: identifying and restraining such wild chaos elementals before harm comes to their hosts or surroundings.
What begins as an instructive family outing turns anything but routine when a mountain search becomes a much more frightening adventure for Penric and his charges. What is undergone there by both mentor and students will yield lessons both unexpected and far-reaching.
***
I'll make my usual spoiler discussion space post tomorrow, for the speed readers.
As always, reader mentions of the new title out and about on the internet and elsewhere are always greatly appreciated, as this blog and word of mouth are the only advertising my indie books get. Amazon always gets plenty of reviews; the other vendors are usually more in need. But no one will see any vendor pages unless they've already heard of the story someplace else, and go to look, so outside reviews and mentions are especially important.
Ta, L.
posted by Lois McMaster Bujold on July, 11
You Can Just Show Up
Jul. 11th, 2025 07:00 pmWhat Is This Magic?
Jul. 11th, 2025 12:12 pm
Via Seattle Aquarium - now, the aquarium didn’t want to just show you a cute picture, they wanted to tell you this:
If you’ve ever been to the Seattle Aquarium, you’ve seen the impact of policy that protects vulnerable species.
Sea otters (like Mishka here) were once on the brink of extinction with as little as 1,000–2,000 otters remaining in the U.S. population. Now, thanks to laws like the Endangered Species Act (ESA), sea otter populations are recovering—but that could change with recent threats to this vital legislation.
Currently, the ESA has saved 99% of species listed on it from extinction. Let's make sure it stays that way. Contact your federal legislators in both chambers of congress and urge them to protect and strengthen the ESA, not weaken it. We've made it easy with three simple steps and a template to follow when contacting your representatives.
I’ll contact my reps if you contact yours!
‘Biblical grounds’ for white Texan divorce
Jul. 10th, 2025 10:15 pmSneak cover peek, Two Tales reprint coming later this summer
Jul. 10th, 2025 09:12 amThe Vorkosigan novella "The Flowers of Vashnoi" has not been available in a paper version since the Subterranean Press edition sold out. The novella "Winterfair Gifts" has had only scattered paper publication, not easy to find. (Both, of course, are continuously available under their own titles as my indie ebooks, or audio downloads from Blackstone.)
Neither would be economically viable for any pro publisher to handle, but it occurred to me they'd be just the thing to add to my little list of print-on-demand paper editions, including The Spirit Ring and "Knife Children". So I've put them together in a single PoD volume, to be titled Two Tales.
Experience with the long-time reader confusion over the novella "The Borders of Infinity" and the 3-novella collection it's in, Borders of Infinity, made me try to label this paper mini-collection as clearly as possible. We'll have to see how it works out. I'm not yet sure how to make it searchable under either of the novella titles, which is what I suspect most people would first be looking for.
Anyway, I asked artist Ron Miller to do us a cover in the style of my other indie VK ebooks, and here's a sneak peek:

When this paper-only edition becomes available to buy, later this summer, I'll post the ISBN number, which should helps folks trying to order it through bookstores. (Uncle Hugo's will certainly have it; they also carry the other two of my PoDs.)
Ta, L.
posted by Lois McMaster Bujold on July, 10
Baby's First Bottle Feeding
Jul. 10th, 2025 12:11 pmVia Alaska SeaLife Center, which writes:
Our cameras were lucky enough to be in our quarantined Wildlife Response area to film Homer boy’s very first bottle feed!
Not all orphaned otter pup patients adjust to taking formula from a bottle well. It’s quite different from suckling milk from their mothers, so it’s always a win for our team (and the otter!) when a pup takes to a bottle quickly. His first time trying the bottle was a little messy, but since then, this little pup has mastered the bottle.
And, of course, dinner is always followed by a swim and a bath!
This little guy, “Homer boy,” is the same from this post from about a week ago.
Hi, hello, I toss this post into your timeline because
Jul. 9th, 2025 02:42 pmHow to win a debate against a transphobe.
Jul. 8th, 2025 10:48 pmAs a former competitive debater and a veteran of many, many Internet debates, I want to share some of my favorite clever comebacks against transphobic talking points. These are just suggestions, of course; feel free to rephrase them in your own words.
They say: “What is a woman?”
Best response: Give a trans woman that makeup you bought and never used. Teach her how to use it if she doesn’t know. Tell her she looks beautiful. Mean it.
They say: “Aren’t you just reinforcing gender stereotypes?”
Best response: Buy gender-affirming clothing and hygiene products for trans people in need via the Transhealth wish list. (Or you can send them items directly, but ask first, they have limited storage space.)
They say: “Why are you letting children make irreversible decisions that they’ll regret later?”
Best response: Send a message of hope and affirmation to trans youth via the Southern Equality Project.
They say: “God made you to be a man/woman.”
Best response: Participate in an online or in-person support group hosted by Keshet (Jewish) or MASGD (Muslim) or Transmission Ministry Collective (Christian) or IQBC (Buddhist).
They say: “LGB people will lose all the progress they made if they don’t drop the T.”
Best response: Organize a day in the park or a movie night with your gay, bi, trans, and otherwise queer friends. Bring snacks.
They say: “There’s only two genders. It’s science.”
Best response: Enroll in the PRIDE study, the first long-term national health study of LGBTQIA+ people. It’s produced a huge amount of science supporting LGBTQIA+ health, and guidelines for healthcare providers to better care for us. They take privacy seriously and have a Certificate of Confidentiality and an organizational commitment to shield their data from legal demands, including from the federal government.
They say: “You’re mentally ill.”
Best response: “If you ever need to talk about serious stuff or just vent, I’m here and I’ll listen and I won’t judge,” to a trans friend who’s not quite close enough to know if that’s something they could ask of you.
They say: “This new social media trend has gotten out of hand.”
Best response: Browse the Digital Transgender Archive and educate yourself about the long and rich history of gender diversity.
They say: “Thank God Trump is finally doing something about this madness.”
Best response: Get into local politics. I mean yeah, sure, call your reps if there’s a chance in hell of them listening, but the places you really can make yourself heard are the town hall, the school board session, the city council meeting. Here’s some important advice on how to more effectively advocate for trans people in these settings.
They say: “It’s not surgery, it’s mutilation.”
Best response: “Do you need a ride home from the hospital? I can come check on you and bring you meals while you’re recovering,” to a trans person planning surgery.
They say: “I hate trans people.”
Best response: “I respect and support trans people.” Not to them. To everyone else. To your coworkers and your classmates and your neighbors and your friends and your Internet friends and anyone you can safely say it to.
They say: “You’re ruining your body.”
Best response: Log off for the night, eat, drink, stretch, read a chapter you love in a book you love, and go to bed on time for once. Caring for the community includes caring for yourself.

you say: hey cliff this post sure sounds all wise and noble but I caught you yelling “well it’s not my problem you go poopie in your pants if everyone on earth doesn’t perform pink and blue at your fucking pleasure, poopiepants” at some rando republican on another site like twenty minutes ago
my response: personal growth is a process
Someone left my cake out in the raid
Jul. 8th, 2025 06:58 pmAll the children of the world
Jul. 7th, 2025 10:56 pmOur Rescued Female Pup Has a Name Now!
Jul. 7th, 2025 12:07 pm



Via Alaska SeaLife Center, which writes:
Our first otter patient admitted in 2025, the young female from Homer, now has a name:
✨Meet Un’a! ✨
Un’a means “that out in the open water” in the language of the Alutiiq/Sugpiaq people. It’s a fitting name for this special pup who has shown strong resilience in her recovery!
See our previous posts here, here, and here - or check out her new tag!
What’s math for anyway
Jul. 4th, 2025 01:44 amWell, spoiler alert… Ranunculus fits just fine. This was not at all a guarantee, despite the rather ridiculous number of times that I checked before binding off and going back to do the neck. I felt compelled to pop back and tell you all how it was fitting, not just because I mentioned that I was worried it was going to be too short, but because the very last picture I posted of it on instagram looked like this.

Let’s back up to how I got there – which I admit was a very dramatic moment – one where I went to pull a finished sweater over my head and lo, it did not go. On the upside, I did stop worrying about the length for a while. Here’s what happened. I told you all in the last post that since I changed the gauge on this sweater (I went down a needle size or so to make a fabric I like better. What the heck, it’s my sweater.) That meant though, that I wasn’t at all sure how many I wanted to cast on for a top down sweater, so I skipped it. I cast on provisionally after the neck, and just started working the sweater. When I was done, I came back, picked up all the stitches, and worked the neckband.
Here’s the thing though. Did I do any figuring? Did I follow up on my original thought and have a little chat with my inner knitter about how I was worried it would be too small because I went down a needle size, and perhaps reflect upon how none of that had changed? Yeah verily, did I look upon the knitting and think “Well Stephanie, this is exactly the moment one knits a swatch for” and having though that, picked up the swatch that I did indeed knit, and count how many stitches it would take to go around my noggin? Did I?
No, gentle knitter, I did not. Even though the swatch sat nearby, even though (sort of unbelievably) I had a tape measure nearby… nope. I just took a look at that neckline and decided to just smash the question with the weight of my experience and thought “Looks right.” and just went for it. It was not right. (See above.)
Anyway, obviously I ripped back the cast on, and all the ribbing, and then I did the math and NOW this sweater both goes over my head and …

It is the right length. I knew it.

Sweater: Ranunculus, Yarn; (Cottage Fingering, 50% Merino, 20% Linen, 15% Silk, 15% Cotton) Modifications, changed the gauge, provisional neckline, fewer stitches for the neckband itself – oh, and I only did the short rows in the back, and I made them wider. It fits me better that way.
For now, I’m off to bed. Jen and I are going on a training ride in the morning, and I have to get up at 5:30am to make it happen, and that is not a thing that is really in my wheelhouse without getting to bed early. If I survive, I’ll pop back and tell you a story about some socks.
(PS. If you wanted to sponsor me or Jen tomorrow to encourage two rather old soft women to ride like the wind, you can do it by clicking on our names. We start to ride at 7, and can use whatever encouragement you can offer. )
Holy Saturday
Jul. 3rd, 2025 09:18 pmAlaska SeaLife Center Has Another Rescued Admit!
Jul. 3rd, 2025 12:16 pmVia Alaska SeaLife Center, which writes:
❗New northern sea otter pup patient admitted ❗
Have you heard the news? There’s another adorable sea otter patient admitted to the ASLC Wildlife Response program! He was first spotted high up on the beach in Homer with no adult otters in sight. After a few hours alone, birds began to approach the vulnerable pup, and the team knew they needed to act. With authorization from the U.S. Fish and Wildlife Service, the ASLC Wildlife Response Team coordinated the pup’s safe transport to Seward for immediate care.
So far, the pup seems to be doing well, and our team is caring for him around the clock.
Read more at ASLC’s website!